Leon Battista Alberti developed
one of the first concepts in machine-assisted encryption in
XV century through the invention of the cipher disc. Basically
it consists of two circular discs, diffferent in diamenter where
the alphabetic scales are engraved. The smaller disc is mounted
concentrically to the larger one in such away when moving the
discs, the alphabetic scales are related among themselves.
Thus, cipher disc provided an easy way to change ciphers merely
by moving the scales; so it was possible to arrange 26 differents
ways to represent a letter, depending entirely on the position
of the inner disc alphabetic scale.
When sending a message, the sender and the recipient would agree
on a cypher key For instance the letter "A" in the
regular alphabet would be positioned next to the
"G" in the ciphered alphabet.
Without a doubt the cipher disc invented by Alberti carved out
the way for the practical use of the polyalphabetic ciphering,
as well as later on inspiring other reseachers to employ his
machine-assisted encryption concept as the one developed by
the American state secretary, Thomas Jefferson in 1795.

The machine-assisted concept invented
by the American secretary of state Jefferson in 1795
Courtesy: National Security Agency USA
The Jefferson machine-assisted encryption consisted twenty-five
wooden discs mounted in a single spindle. On each disc the
twenty-six letters of the alphabet were written in a jumble
order in such a way that the order on each disc was different.
In spite of such advanced machine-assisted encryption concept
it was not quite well- understood for the moment and so, its
resurgence came out one century later by the researches of
the French cryptologist Etienne Bazeries.
Known as Bazeries cylinder, it consists of a set of roughly
20 to 30 numbered discs with a different cipher alphabet on
the edge of each disc, and a hole in the centre of the discs
to allow them to be stacked on a spindle. The discs are removable
and can be mounted on the spindle in any desired order. So,
the order of the discs can be considered the cipher key for
the Bazeries cylinder, which could be arranged the discs in
the same predefined order.
In order to encode the message, the plain text is spelled
out in one row of disc whose order was previously selected.Then
the user can copy any row of text on the discs other than
the one that contains the message. The recipient simply has
to put the discs in the agreed-upon order, spell out the encrypted
message by rotating the discs, and then look around the rows
until the plaintext message could be read.
The only advantage that those relatively simple devices had
over traditional ciphers was speed.
However, as afore seen considering the urgency of the plain
text enciphering, generally required by the substantial volume
of military communications, very soon armies and armed forces
felt the necessity to employ new types of machine-assisted
encryption.
In this way just after the WWI, that kind of machine was made
in several countries and around 1935 they reached a high level
of efficacy.
Most were German or Swiss -made and generally automated a
polyalphabetic substitution concept with extremely long cipher-key
using several hundred thousand incoherent series of letters.
They were supplied in several types. While the smaller ones
were manually operated and did not print out messages, the
larger models were electric operated and had a typewriter
keyboard like the ones used in a standard office typewriter
machine.
In the later thirties most of the great nations had machine-assisted
encryption systems some of them in a compact, size similar
to a portable typewriter.

Machine-assisted encryption in a compact size similar to a
portable typewriter at the end of WWII.
Courtesy: Antonio Fucci Collection.
During the WWII, was developed machine-assisted encryption
systems using teletypewriting facilities connected to an automatic
ciphering box. Among the most famous one is the Japanese machine-assisted
encryption known by the codename "PURPLE".

The famous machine-assisted encryption
developed by the Japanese known by the codename Purple.
Courtesy: National Security Agency USA.
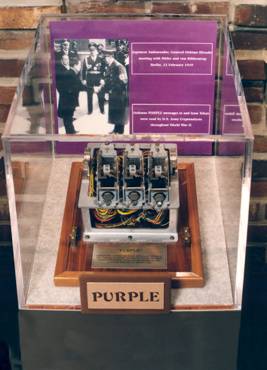
Fig. 215 a 6 - Display showing
the eletromechanical operation encryption keys used in the
Purple mahcine.
Courtesy: National Security Agency USA
However, all the codes and cyphers as well as the machine-assisted
encryption aforementioned still used a logical system known
as symmetric key algorithms in which the same cryptographic
key is selected with the underlying algorithm by both the
sender and the recipient, who must both keep it secret.
| Algorithm (al-Khwärizmï),
in simple words it consist in a set of well-defined instructions
for accomplishing some task. Its Etymology is related
with the surname of the Persian mathematician Abu 'Abd
Allah Muhammad ibn Müsä al-Khwärizmï.
|
In mid seventies a new encryption system known as asymmetric
key algorithms fundametally changed the way cryptosystems
might work. In such new system it uses a pair of mathematically
related keys, each of which decode the encrypted message performed
using the other. Some, but not all, these algorithms have
the additional property that one of the paired keys cannot
be deduced from the other by any known method other than trial
and error.
Furthermore, for a known encrypted messsage using such an
algorithm, only one key pair is needed per user. So, by designating
one key of the pair as private, that is always considered
as secret, and the other as public domain, no secure channel
is needed for key exchanging. Whereas the private key stays
unknown, the public key can be widely used for a very long
time without compromising its security, making it safe to
reuse the same key pair indefinitely.
Thus, by using the asymmetric key algorithm it is possible
a secure communication through an insecure channel.
It is interesting to note that in adopting this new cryptosystem
developed in conjunction by Whitfield Diffie and Martin Hellman
in 1976 it brought the principle of encyphering squarely into
the public domain and in turn broke the near monopoly on cryptography
held by government organizations worldwide.
Nowadays, the enciphering public domain can be found in several
modern technological advancements. Among them are: the enciphering
system A5/1 and A5/2 used in cell phone operating in the GSM
technology; Content Scramble System (CSS) for encrypting and
controlling recorded data in products such as DVD or digital
video discs .
|